Ransomware Attacks in 2022 – Protect Yourself

It’s 2022, and the onslaught of ransomware attacks on Australian organisations is more prevalent than ever. Ransomware threats and costs are on the rise, and the cybercriminal organisations that use ransomware are causing real and long-lasting damage to governments, small businesses, enterprises and individuals alike.
Ransomware is a type of malware or malicious software that holds data “at ransom” until the hackers get what they want. Usually, that’s payment through Bitcoin (the reason hackers prefer this payment method is that as opposed to trackable bank accounts, cryptocurrency is really hard to trace).
Due to our high per-capita wealth and online presence, Australia has become a particularly lucrative target for ransomware groups, and the Australian Cyber Security Centre (ACSC) considers it our “highest cyber threat.”
What are ransomware attacks?
The Ransomware Payments Bill 2021 (withdrawn from Parliament) defines a ransomware attack as “when an unauthorised person knowingly accesses, modifies or impairs data, or impairs electronic communication to or from a computer and demands payment to do certain things including to undo damage or prevent the publication or exfiltration of data.”
Typically, hackers deposit malicious software into IT systems via phishing attacks or email scams or by the victim unknowingly downloading malicious software.
What are the types of ransomware attacks?
Crypto ransomware (encryptors)
Traditionally, ransomware was a simple business model. The malicious software would encrypt the victims’ files and make them pay to decrypt (unlock) them.
However, as the organisations began to implement backup strategies, this type of extortion has lost its efficiency. Businesses can simply restore the locked information from their backup, without the need to pay the hacker to decrypt them. This has prompted ransomware criminals to come up with new ways to extort.
Ransomware 2.0 (double extortion ransomware)
In 2020, at the dawn of a new decade and a global pandemic – that brought with it even more reliance on online services and software – ransomware 2.0 showed up. It works by firstly stealing the data and then encrypting it. This is a double extortion tactic: if you don’t pay, they publish the data on the dark web (extortionware).
Triple extortion ransomware
Then, towards the end of 2020, ransomware groups began implementing triple extortion tactics. – by requesting payments from all the people whose data they have stolen from the initial victim. This essentially makes anyone vulnerable to ransomware. You could be a very internet security-savvy individual, but if the company that holds your data is susceptible to an attack, you could find yourself a victim, with hackers requesting money from you.
The healthcare industry is a wildly exploited industry, and very lucrative when it comes to triple extortion. Think about before and after photographs of plastic surgery for example. Hackers will play on the embarrassment level of the patient and request payment from both the clinic from which it has stolen data as well as from its patients.
Ransomware attacks implications
In 2022 ransomware families are so organised, that ransomware-as-a-service (RaaS) is widespread. RaaS is a pay-for-use malicious software that hackers sell to customers called affiliates. It’s an illegal service developed by organised cybercriminal groups.
Top ransomware and groups 2022
- LockBit
- Conti
- BlackCat
- Clop
- AvosLocker
- Hive
- HelloKitty
- BlackByte
- Dharma
- Ryuk
- Djvu
Examples of ransomware
Ransomware attacks have been around for decades, but have become more organised and damaging with the growth of the cyber landscape.
One of the most targeted industries is the healthcare industry. The healthcare sector is one of the most lucrative for cybercriminals – and one of the most damaging for its victims.
A particularly damaging attack was done by the Conti ransomware gang in 2021 affecting Ireland’s Health Services, in what was dubbed by the FBI “the costliest strain of ransomware ever documented.” In 2022, Hive attacked the Costa Rican healthcare systems – after an already devastating attack by Conti on the Costa Rican Government.
In 2021, Darktrace reported that cyber attacks on healthcare in Australia doubled during that year, with the industry still the most attacked in 2022.
Recently, other ransomware victims in Australia include JBS Foods and Nine Entertainment.
What is a famous ransomware attack?
The biggest ransomware attack of all time happened in 2017 through malware known as WannaCry – which affected over 150 countries.
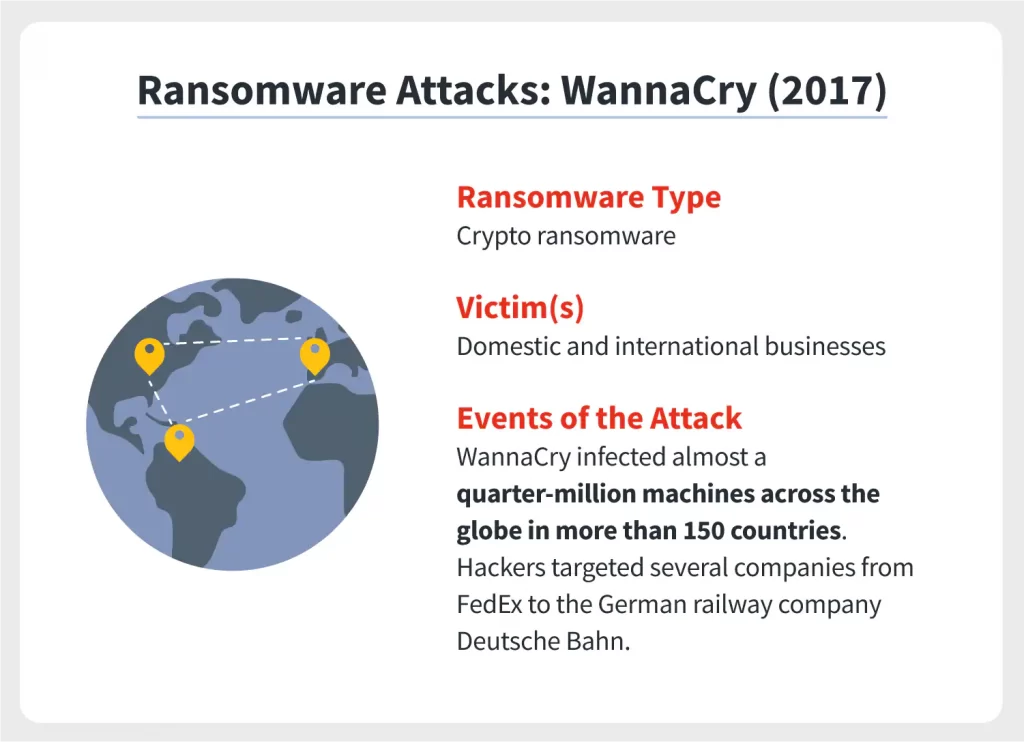
WannaCry ransomware attack implications. Source: Norton.
How many ransomware attacks occurred in 2021?
According to The State of Ransomware 2022 by Sophos, 80% of Australian organisations surveyed were hit with ransomware in 2021. Globally, the number of ransomware attacks in 2021 was reported to be 37%.
What are signs of ransomware attack?
If malware has bypassed your security, there are a few common signs that can help you identify a ransomware attack:
- You can’t log in to your devices – your password or logins don’t work
- Files have been renamed and/or have unusual extensions
- Explicit pop-ups appear requesting payment to unlock files
- You notice unauthorised data extraction
How to protect yourself against ransomware attacks
To protect yourself against ransomware attacks, your organisation needs to set up a few best practices in place.
- Most ransomware attacks start via email. Update your security policies and educate your employees to stay vigilant and don’t open/click on/download anything that looks suspicious.
- Map your attack surface. Find out where your system vulnerabilities lay and reduce their surface.
- Stay on top of your IT security. Constantly update your software, patch vulnerabilities and have up-to-date anti-virus software installed.
- Backup your data. Have regular backups in place and store this data off-network to keep it protected in case of a breach.
- Restrict users’ permissions. The best approach to employee authorisation is a zero-trust approach. Use multi-factor authentication. Also, make sure you delete any inactive user accounts that could be exploited by criminals.
- Leverage expertise. Be in contact with a trusted expert such as a managed service provider that can help you assess your security as well as with the recovery process in case of an attack.
Don’t let your organisation be a victim of ransomware attacks
As you can see, ransomware damage costs organisations dearly in 2022, through data breaches that disrupt global networks, affect individual lives, and can ruin the reputation of an enterprise. Having a ransomware incident response plan in place is essential for businesses of any size.
Don’t be a victim. Whereas it’s impossible to fully prevent an attack on your organisation, you can get cyber insurance to protect your business from liability, and work on a cyber resilience strategy with your managed service provider.
Now more than ever it’s essential to have mitigation strategies in place that reduce the opportunity of an attack. While ransomware decryptor tools exist, they won’t protect you from triple extortion.
The landscape moves very quickly, cyberattacks get more and more sophisticated so your organisation needs to constantly be on top of its ransomware protection applications and IT security policies. Contact us today and we can conduct a free audit and help create a layered approach that will help prevent ransomware attacks, build resilience and keep your organisation safe.
